
Operational technology (OT) cybersecurity is a hard but critical part of guarding organizations’ vital techniques and means. Cybercriminals no lengthier break into systems, but rather log in – producing accessibility security far more complex and also a lot more crucial to manage and manage than ever just before. In an effort to resolve the accessibility-related troubles going through OT and critical infrastructure operators, the crew at Cyolo designed a zero-have faith in accessibility platform intended to meet up with the distinctive protection, security, and uptime necessities of OT and industrial control devices (ICS) environments.
Let’s appear under the hood:
The Cyolo alternative is a large-driven combination of Zero Rely on Network Obtain (ZTNA), Identity Supplier (IdP), and Privileged Obtain Administration (PAM). What can make this solution stand out from the pack is that other ZTNA methods do not present IdP or PAM capabilities, when Id and Access Administration applications (IdPs and PAMs) do not extend connectivity. And compared with other gamers in the secure distant access room, Cyolo does not involve a cloud connection or the installation of an endpoint agent. This permits the platform to deal with some challenging connectivity use situations that lots of corporations battle with.
How the Cyolo Platform Works
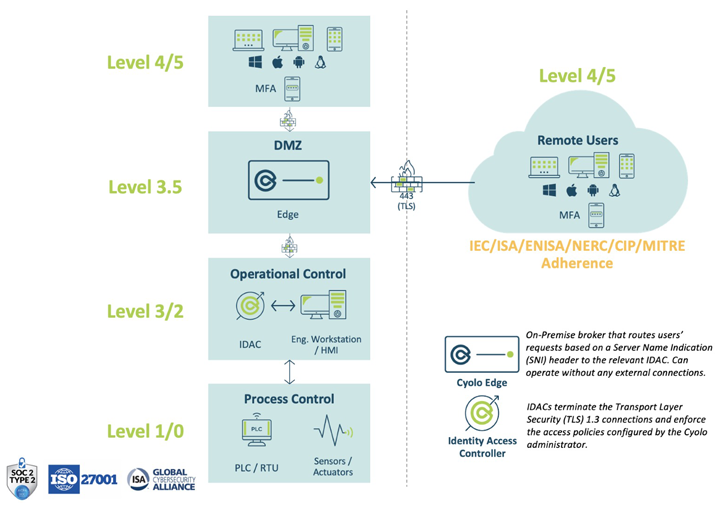 Determine 1: Architectural layout of a Cyolo deployment
Determine 1: Architectural layout of a Cyolo deployment
The main creating blocks of the Cyolo system are Identification Accessibility Controllers (IDACs) and Edges.
- Identification Entry Controller (IDAC): IDACs terminate the Transport Layer Security (TLS) 1.3 connections and enforce the entry procedures configured by the Cyolo administrator. As a ‘reverse-proxy,’ all decryption and enforcement manifest guiding organizational firewalls.
- Edge Brokers: Edges are on-premises brokers that route users’ requests dependent on a Server Identify Indicator (SNI) header to the pertinent IDAC. In all deployment types, the Edge routes targeted traffic from the consumers to the IDACs. Notably, Edges can operate with no any external connections and never ever decrypt any site visitors, creating Cyolo a scarce zero-have confidence in obtain answer that actually adheres to the principles of zero believe in.
Cyolo can be deployed on-premises, in a SaaS product or, most typically, in a hybrid variation of the two. The on-premises parts can be totally isolated and non-IP linked for extra security, as needed. These are the core aspects needed for each and every deployment process:
- IdP Connection: Identification providers (IdPs) make certain the person trying to get entry is who or what they claim to be throughout various platforms, purposes, and networks. Cyolo can integrate with your existing IdP, or you can use Cyolo’s community IdP that is incorporated as component of the IDAC set up. The IDAC connects directly to the IdP (not as a result of the Edges).
- IDAC Outbound Interaction: IDACs constantly connect outbound, irrespective of whether they link users’ sessions coming from the Edges (on port 443) or whether or not they talk with the posted applications they provide (on their certain port).
Products Deep Dive and Differentiation
Now, let us take a deeper seem into the Cyolo system and see what distinguishes it from present strategies to accessibility security and other resources on the current market.
At initially look, the platform has a clean and easy to navigate person interface. It is established up to handle and administer the accessibility of customers to distinct applications, and it brokers this accessibility by using a established of zero-have confidence in procedures. Looking a little bit more, it logs lots of information about all user action and has a sturdy software programming interface (API).
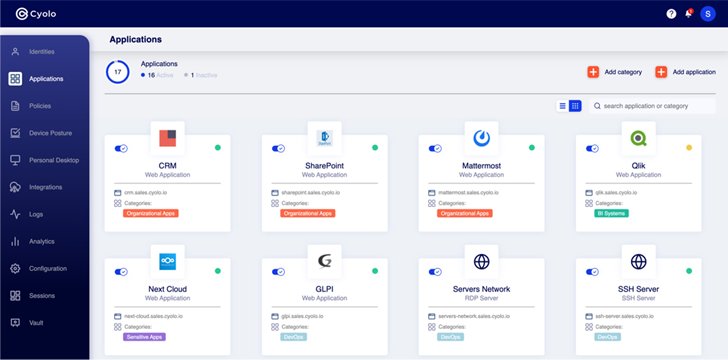 Determine 2: Most important web site on the Cyolo administrator dashboard
Determine 2: Most important web site on the Cyolo administrator dashboard
Id: The Cyolo system can act as a standalone identification resource with users being additional through file import, Procedure for Cross-domain Identity Administration (SCIM), or person self-enrollment. This is particularly valuable when onboarding third-celebration suppliers and contractors who you may well not want to increase to your company’s IdP. Each user can be additional to unique teams, which are made use of to grant entry to unique programs or services, primarily based on insurance policies. The workflow to incorporate customers is uncomplicated and further authentication steps, such as multi-variable authentication (MFA), can be included as a prerequisite.
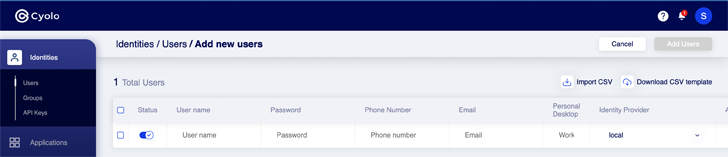 Determine 3: Including a new person in the Cyolo dashboard
Determine 3: Including a new person in the Cyolo dashboard
Cyolo can also perform with all common IdPs, such as Okta, Active Listing, Azure Ad, Ping, etc. If providers have several IdPs, Cyolo can federate them and allow for the most suitable IdP for a unique entry ask for to be used.
Apps: Cyolo supplies connectivity to all programs dependent on legitimate identification, and then inserts qualifications on behalf of the consumer to help a full Solitary Indication-On (SSO) encounter. This simplifies the log in process for buyers and can help eradicate the need for generic accounts or shared passwords, which can build extra risk.
Cyolo can also increase secure entry to legacy and personalized-built purposes to allow MFA and SSO for these demanding means. This functionality is most useful in the OT sector, which relies upon intensely on older tools and techniques that do talk with Security Assertion Markup Language (SAML) or OpenID Hook up (OIDC).
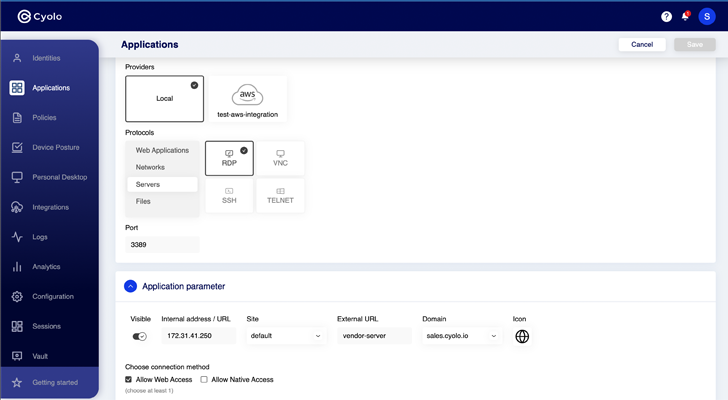 Figure 4: Configuring programs in the Cyolo system
Figure 4: Configuring programs in the Cyolo system
Insurance policies: Every application is configured to need unique access parameters that account for person end users and teams, alongside with contextual particulars these types of as time of working day or place. Two interesting functions are the capacity to call for approval prior to accessibility and the enforcement of recording for every single obtain session.
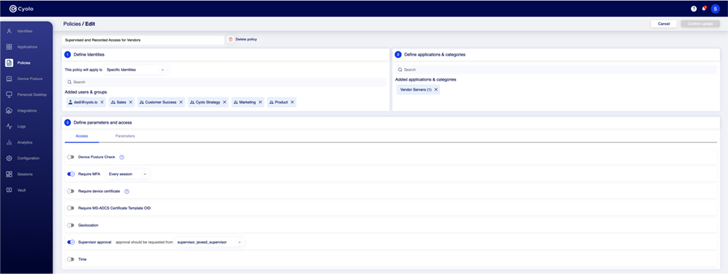 Determine 5: Configuring procedures among identities and programs in the Cyolo system
Determine 5: Configuring procedures among identities and programs in the Cyolo system
Logs: All action on the system is tracked in an conveniently exportable log. This is specially handy when the Cyolo software is offering SSO for an software that ordinarily employs a generic username and password. Moreover, simply because Cyolo includes a password vault, it can securely retailer and rotate the shared password, with the log monitoring accurately which person accessed the software or assistance.
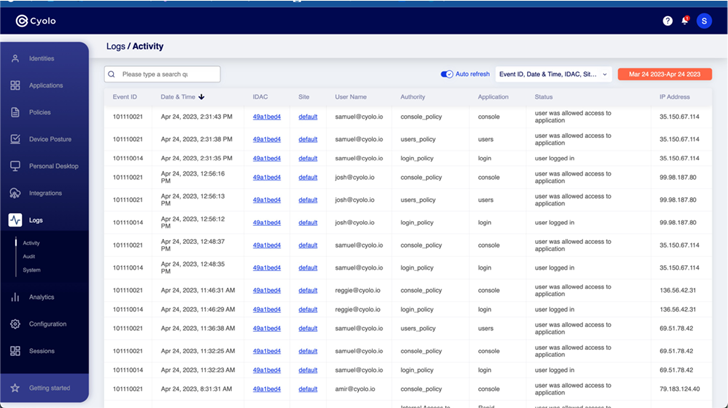 Determine 6: Exercise log inside the Cyolo system
Determine 6: Exercise log inside the Cyolo system
Supplemental Observations:
- Simply because Cyolo does not require a cloud relationship to run, the option is ideal for firms who require to isolate critical segments of their network and limit access to them. This is prevalent for OT/ICS operators who want to tightly control distant and 3rd-social gathering accessibility into these regions.
- Remote access is occasionally hampered due to the fact the security device calls for an agent to be set up on an endpoint product. Cyolo does not need an agent to work, creating it quick to use for 3rd get-togethers, exterior contractors, or small business companions.
- Their IDACs and Edge are containerized program programs (Docker containers), so they can be loaded on to a range of kind things, these kinds of as digital machines or hardened servers. This tends to make deployment straightforward and quickly, as there is no want to interrupt site visitors to install.
Conclusions
It can be clear that the Cyolo staff recognizes the value of a good, simple person knowledge. Right after all, any security or access resource have to be quick for conclude buyers if it is to have any hope of achieving highest adoption.
When an conclude consumer logs in to the Cyolo system, they see only the applications, methods, and applications they need to have to execute their perform. This is configured dependent on the polices for their identification and the unique software they are accessing and is enforced at the IDAC level within the organization’s reliable boundary. Right after the person selects the application they want to access, the Cyolo system will regulate all the connectivity and credential insertion for a rapidly and comprehensive SSO expertise. The elegance of this is that the user’s workflow is not impacted (in some established-ups, the user may perhaps not even know they’re employing the Cyolo platform at all), yet the gain to security posture is considerable.
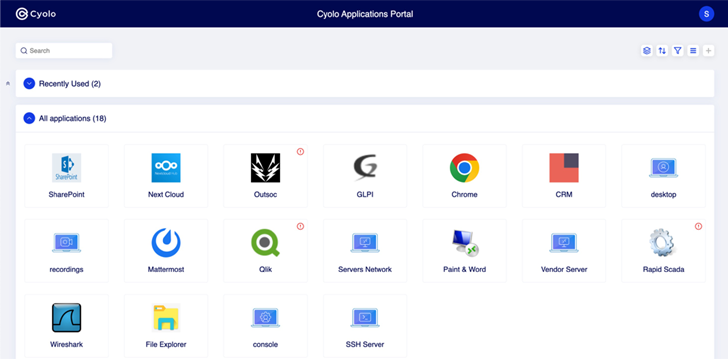 Determine 7: Cyolo Stop-Person Applications Portal
Determine 7: Cyolo Stop-Person Applications Portal
Just one further attribute worth noting is the Cyolo platform’s administration of Remote Desktop Protocol (RDP) connections into OT environments. With Cyolo’s skill to act as an IdP, adding an external (3rd-social gathering) person was quite quick. Layering additional security layers, like MFA, supervisor approval, and complete audio/visible recording, have been intuitive to set up and supply a beneficial document of a user’s activity though connected. These abilities exhibit the energy of integrating connectivity with IAM procedures.
This quick demo demonstrates aspect-by-facet person and admin screens to illustrate the workflow for a Native (or Web) RDP session with supervised access and recording.
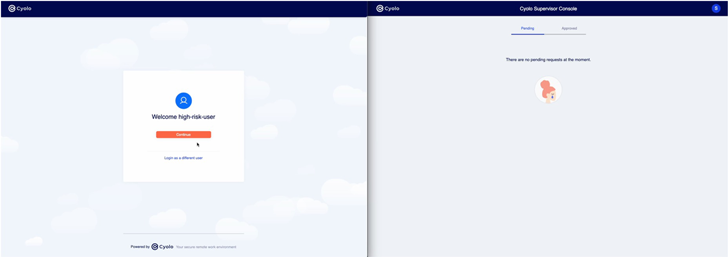 Online video 1: Speedy demo of supervised access, without the need of an agent, to a distant desktop by means of RDP
Online video 1: Speedy demo of supervised access, without the need of an agent, to a distant desktop by means of RDP
General, the Cyolo system is a functional tool that can assist fix some of the far more challenging use instances plaguing numerous security operators today. By focusing on connectivity, id validation, and entry administration, Cyolo delivers a ton of horsepower to the desk. And the most effective part is that they do not go away any software or assistance out and they specialize in tough eventualities, these types of as vendor accessibility to OT environments. If you have a challenge that has been challenging to clear up, it may possibly be time to give Cyolo a nearer look.
To find out additional about Cyolo, simply click here.
Identified this article attention-grabbing? Abide by us on Twitter and LinkedIn to read through far more distinctive written content we post.
Some parts of this article are sourced from:
thehackernews.com


 CopperStealer Malware Crew Resurfaces with New Rootkit and Phishing Kit Modules
CopperStealer Malware Crew Resurfaces with New Rootkit and Phishing Kit Modules