Ransomware affiliate marketers linked with the Qilin ransomware-as-a-assistance (RaaS) plan gain anyplace concerning 80% to 85% of the ransom payments, in accordance to new findings from Group-IB.
The cybersecurity firm claimed it was ready to infiltrate the team in March 2023, uncovering aspects about the affiliates’ payment composition and the inner workings of the RaaS plan adhering to a personal conversation with a Qilin recruiter who goes by the on line alias Haise.
“Lots of Qilin ransomware attacks are personalized for just about every victim to maximize their impression,” the Singapore-headquartered corporation claimed in a new report. “To do this, the risk actors can leverage these techniques as switching the filename extensions of encrypted files and terminating precise processes and products and services.”
Qilin, also recognised as Agenda, was first documented by Craze Micro in August 2022, setting up off a Go-based mostly ransomware before switching to Rust in December 2022.
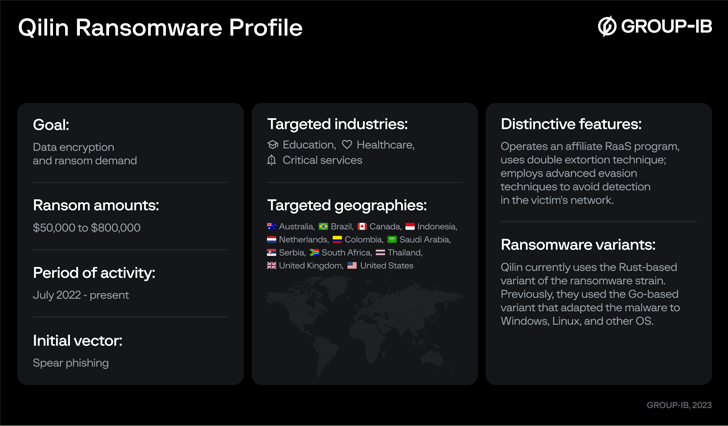
The adoption of Rust is also significant not only because of evasion detection capabilities, but also for the point that it lets the risk actors to concentrate on Windows, Linux, and VMware ESXi servers.
Attacks mounted by the group make use of phishing email messages that contains malicious back links as a indicates to get hold of first entry and encrypt sensitive details, but not before exfiltrating it as part of a double extortion product.

Knowledge from as many as 12 different providers have been posted on Qilin’s info leak portal on the dark web between July 2022 and May possibly 2023.
The victims, which predominantly span critical infrastructure, education and learning, and health care sectors, are positioned in Australia, Brazil, Canada, Colombia, France, Japan, Netherlands, Serbia, the U.K., and the U.S.
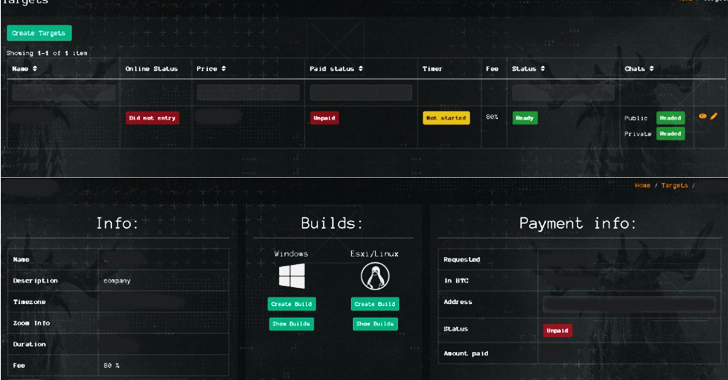
Team-IB claimed the Qilin actors also give affiliate marketers – who are recruited to discover targets of desire and phase the assaults – with an administrative panel to properly oversee different sections of their operations.
“Qilin ransomware group has an affiliate panel divided into sections these kinds of as Targets, Blogs, Stuffers, Information, Payments, and FAQs to deal with and coordinate its network of affiliates,” security researcher Nikolay Kichatov claimed.
- Targets – A segment to configure ransom notes, documents, directories, and extensions to be skipped, extensions to be encrypted, processes to be terminated, and the mode of encryption, amongst other folks
- Blogs – A part for affiliates to build blog posts with information and facts about attacked corporations that have not paid the ransom
- Stuffers – A segment for the danger actors to produce accounts for other users of the crew and regulate their privileges
- News – A segment to write-up updates associated to their ransomware partnerships (at the moment blank)
- Payments – A section that incorporates transaction information, affiliate wallet balances, and options to withdraw illicit proceeds
- FAQs – A area showcasing guidance and documentation facts that information the measures to use the ransomware
“While Qilin ransomware gained notoriety for concentrating on critical sector organizations, they are a menace to companies throughout all verticals,” Kichatov stated.
“In addition, the ransomware operator’s affiliate plan is not only introducing new members to its network, but it is weaponizing them with upgraded equipment, approaches, and even support shipping and delivery.”
Identified this post fascinating? Abide by us on Twitter and LinkedIn to browse more exceptional articles we write-up.
Some parts of this article are sourced from:
thehackernews.com

 Cyolo Product Overview: Secure Remote Access to All Environments
Cyolo Product Overview: Secure Remote Access to All Environments